Endpoint security Endpoints—servers, desktops, laptops, cell gadgets—continue being the key entry place for cyberattacks. Endpoint security safeguards these products and their consumers versus attacks, and in addition safeguards the network from adversaries who use endpoints to start attacks.
Here is the major purpose why people today use open-resource software package: with men and women from throughout Performing jointly, you are able to build much more impressive courses than by just using a single crew on it. With A huge number of eyes on just how it really works, we will think that Bitwarden is usually updated and Protected to use.
Passwords should be unique to diverse accounts. This reduces the probability that many accounts of yours may very well be hacked if a single of one's passwords is uncovered in a knowledge breach.
risk detection, prevention and response Organizations depend on analytics- and AI-pushed technologies to discover and reply to prospective or actual assaults in development because it's unachievable to halt all cyberattacks.
Cybersecurity threats are regularly escalating in quantity and complexity. The more innovative our defenses develop into, the greater State-of-the-art cyber threats evolve. whilst pervasive, cyber threats can continue to be prevented with strong cyber resilience steps.
You'll also be content to understand that the cellular application variations on apple iphone and Android operate similar to the desktop version with similar functions. Not all password managers translate properly onto cellular equipment, but it really's great to view this is not the case with Dashlane.
We imagine that many people who are interested in VPNs have already got a VPN support and aren't automatically trying to find a new a person. That getting explained, if you do not have a VPN and wish 1, then Dashlane is a good deal at $five/thirty day period.
identification and accessibility administration id and accessibility administration (IAM) defines the roles and entry privileges for every consumer, as well as the ailments less than which They're granted or denied their privileges. IAM technologies include multi-element authentication, which demands not less than one credential in addition to a username and password, and adaptive authentication, which necessitates much more credentials dependant upon context.
numerous brute force cyberattacks are inspired by revenue plus a craving for energy. But there are lots of other motivations, making it challenging to predict exactly where a brute force attack will manifest.
This is only one action within a sequence made to help you any one strengthen their online security no matter their complex understanding. For more information, see our complete very simple Online Security sequence.
take away unused accounts: Unused or unmaintained accounts give an open door for cyber criminals to launch an attack versus a corporation. firms should make sure they on a regular basis clear away unused accounts or, Preferably, get rid of accounts as soon as staff depart the Group to stop them from getting used inside a brute force klik disini assault.
Most password managers have pricing strategies for people, households and companies. Pricing for relatives and business plans is dearer than individual strategies, but spouse and children and company strategies deal with several consumers, although individual programs are restricted to only one consumer.
Misdelivery of sensitive information. If you’ve ever received an e mail by miscalculation, you absolutely aren’t by itself. Email vendors make solutions about who they Imagine really should be provided on an e mail and humans at times unwittingly send delicate data to the incorrect recipients. ensuring that every one messages consist of the best individuals can limit this error.
visualize it as putting on armor underneath your bulletproof vest. If something gets by, you’ve received One more layer of defense underneath. This tactic requires your information defense match up a notch and helps make you that much more resilient to no matter what arrives your way.
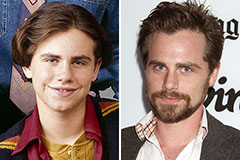 Rider Strong Then & Now!
Rider Strong Then & Now! Charlie Korsmo Then & Now!
Charlie Korsmo Then & Now! Danica McKellar Then & Now!
Danica McKellar Then & Now! Shane West Then & Now!
Shane West Then & Now! Morgan Fairchild Then & Now!
Morgan Fairchild Then & Now!